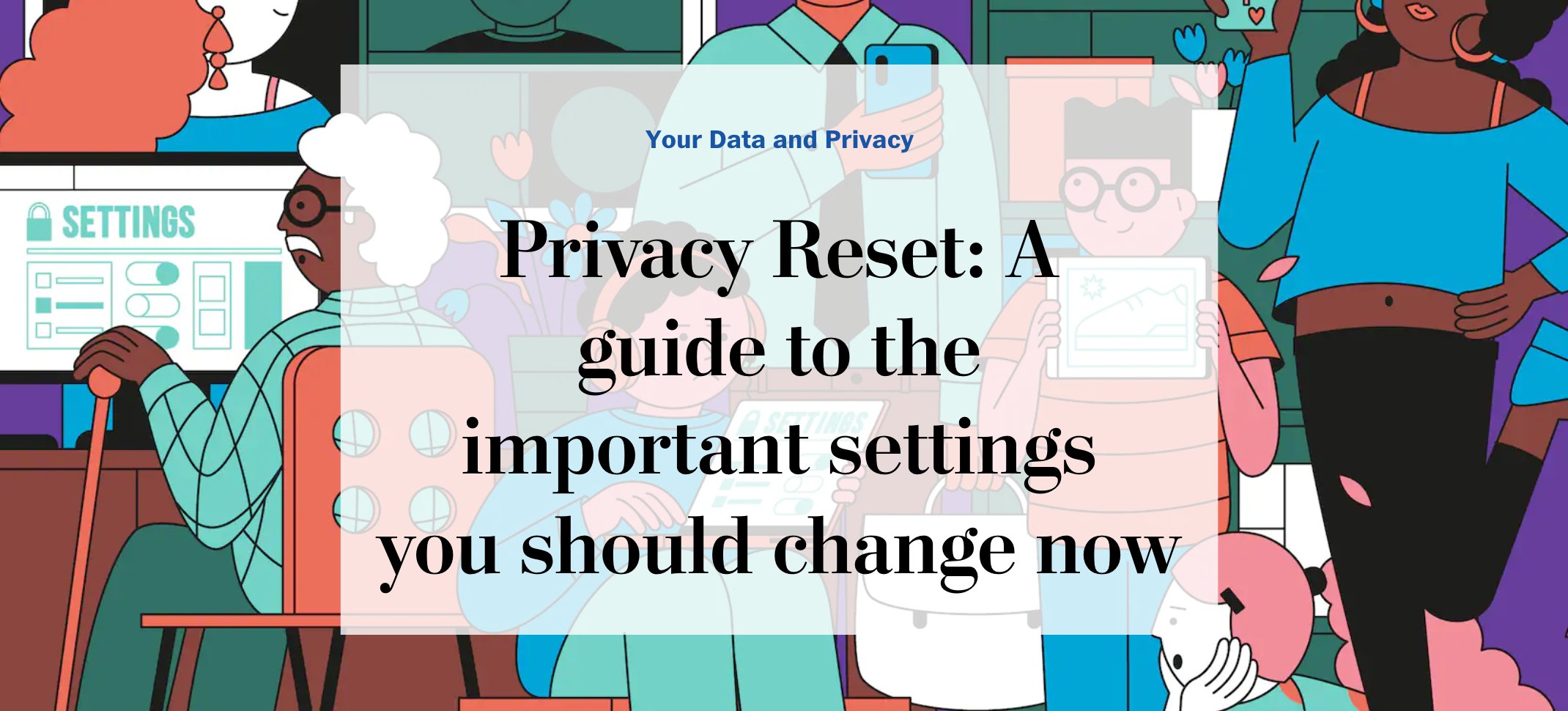
Privacy Reset: A guide to the important settings you should change now
#digital #privacy #cybersecurity
wapo.st/3rjsN5x via
Search timeline
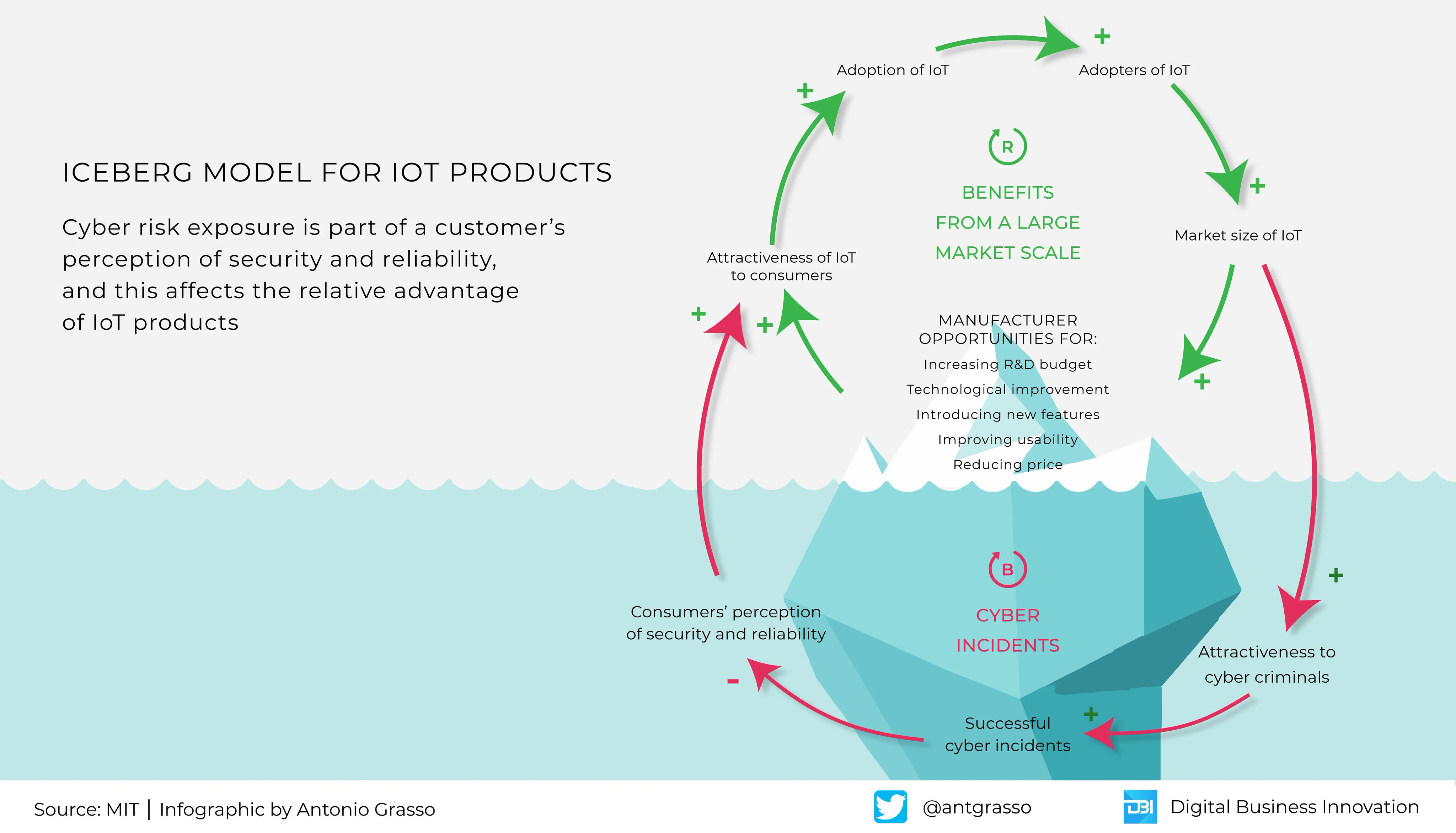
Cyber Security, particularly for IoT devices, passes through appropriate actions implemented by manufacturers. Knowing what is happening is like an iceberg: only the tip can be seen.
Microblog & social design by #CyberSecurity #IoT #IIoT
1
78
119
17
108
1.3K
5 Security Features We Wish Were Included in WordPress blog.wpsec.com/security-featu
#cybersecurity #2FA #FIDO #AuditLogs #CAPTCHA #SSL #TLS
3
76
783
People
Follow
Latest #cybersecurity news; managed by . Do not report hacking or other cyber incidents here. Submit info at us-cert.cisa.gov/report
The National Cybersecurity Alliance is a nonprofit that empowers people to use technology safely & securely. Co-leads Cybersecurity Awareness Month
Official Twitter page of the Canadian Centre for Cyber Security. En français: .
 cse-cst.gc.ca/en/about-terms…
cse-cst.gc.ca/en/about-terms…
 cse-cst.gc.ca/en/about-terms…
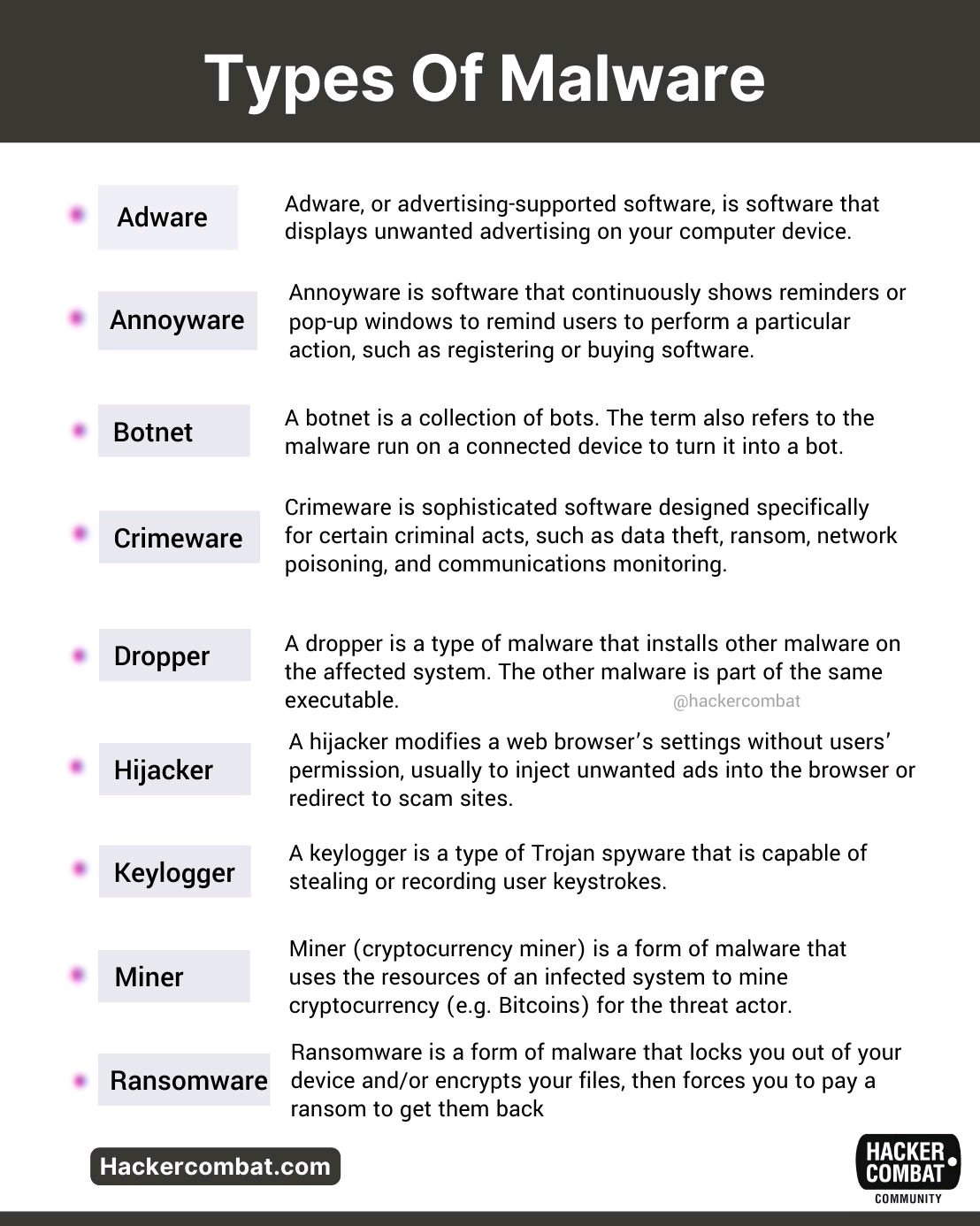
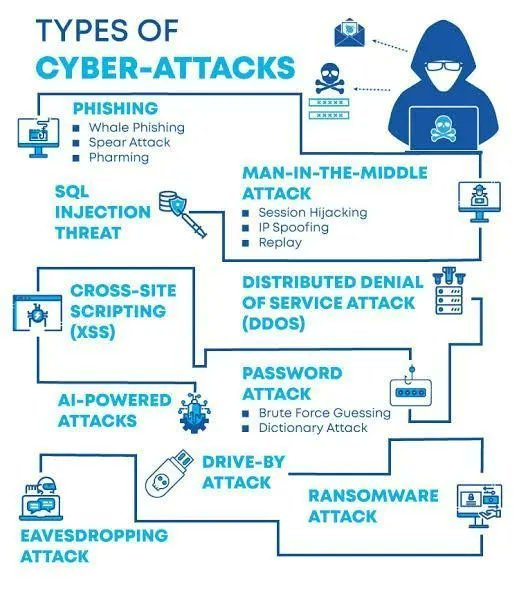
cse-cst.gc.ca/en/about-terms…A classic: Types of cyber attack
#Infosec #CyberSecurity #CyberAttack #Hacking #Privacy #Threat #Malware #Ransomware #Cyberwarning #Phishing #SpyWare
#Tech #Technology
5
211
295
8 different techniques to Bypass Rate Limits in Web Applications and API's.
[A Thread 🧵]
#bugbounty #bugbountytips #cybersecurity #AppSec
2
238
537
Show this thread
Cyber Security Internships 2022 (Remote and Onsite)
github.com/paralax/awesom
#cybersecurity #internship #Job #Jobs #remotework #BugBounty
60
129
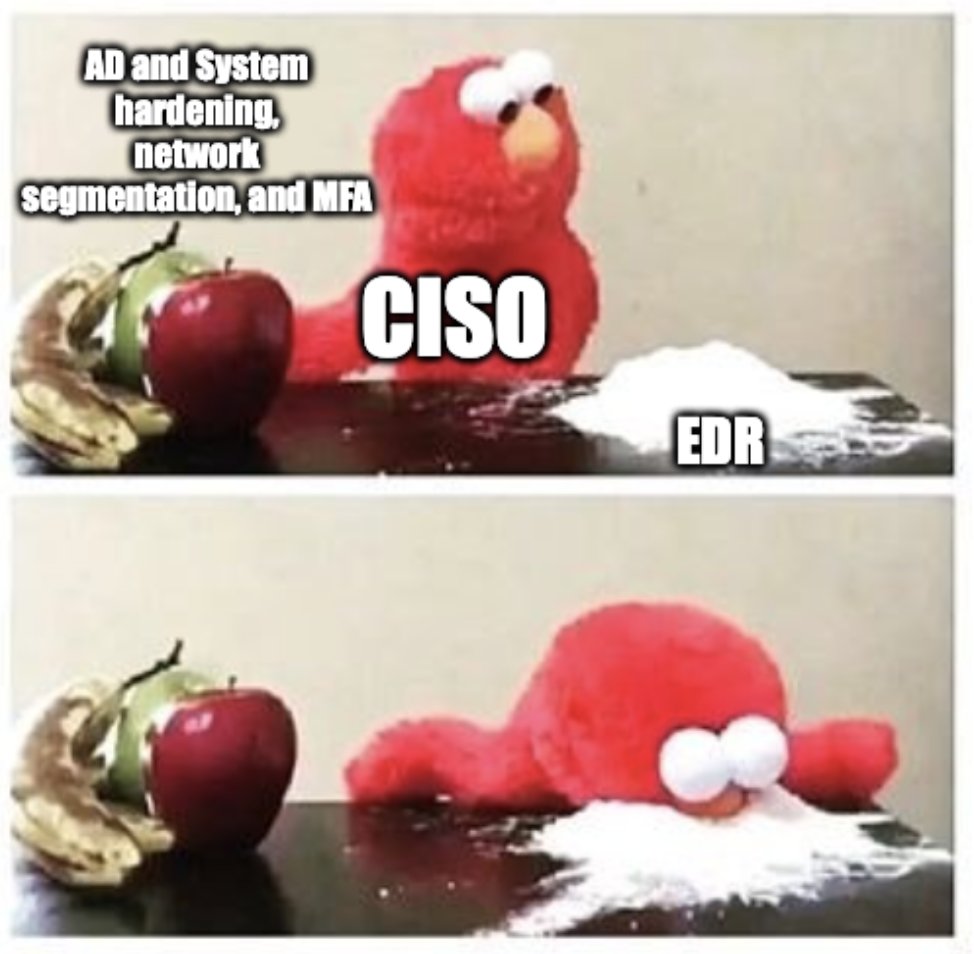
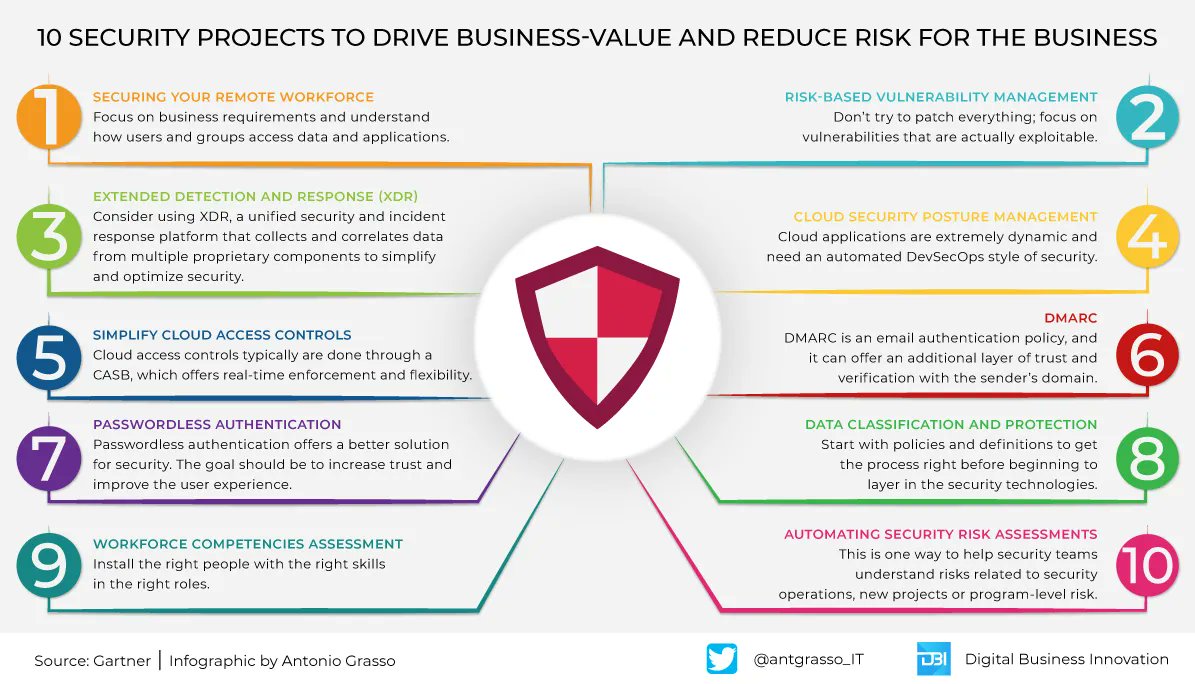
We shouldn't think about cybersecurity in our company as a monolithic block to be addressed as a whole. The best way is to divide the problem into small projects by solving them one at a time.
Microblog & social design by #CyberSecurity #DataProtection
4
108
151
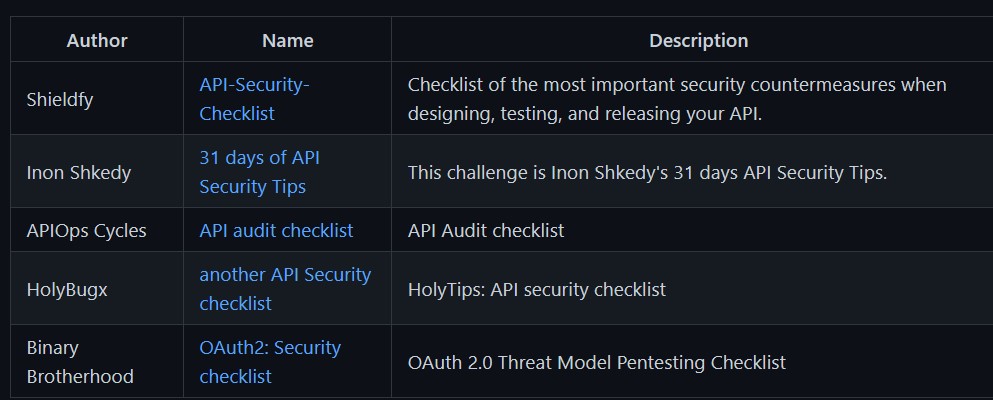
A collection of awesome API Security tools and resources.
github.com/arainho/awesom
#cybersecurity #apitesting #bugbounty
3
279
615
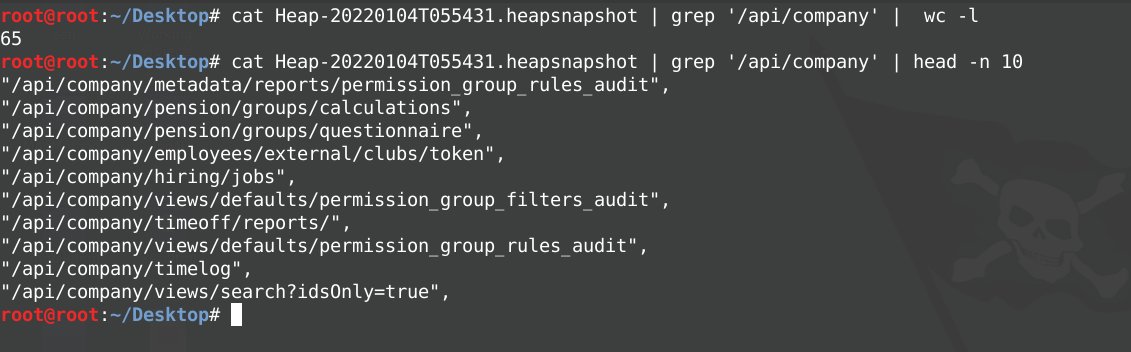
Using chrome heap snapshots to find hidden API Endpoints:
- Open Chrome developer toolkit
- Go to Memory Tab and Click Record Button
- Save the Snapshot and start grepping stuff
Example : cat Heap-xx.heatsnapshot | grep '/api'
#BugBounty #bugbountytips #CyberSecurity
9
189
502
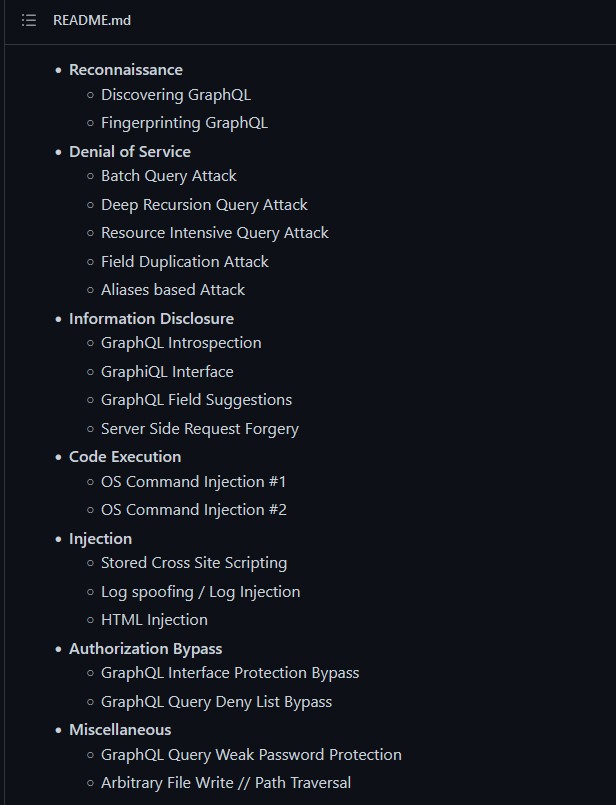
Damn Vulnerable GraphQL Application is an intentionally vulnerable implementation of Facebook's GraphQL technology, to learn and practice GraphQL Security.
github.com/dolevf/Damn-Vu
#hacking #graphql #cybersecurity #bughunting
2
115
296
How do you approach investigating computer security incidents?
Some useful tools worth having your IT staff get familiar with.
ProcMon
ProcessExplorer
AutoRuns
Wireshark
Log-MD
ProcDOT
#infosec #cybersecurity #MalwareAnalysis #DFIR
20
114
382
Show this thread
Do you want to level up your mobile #hacking skills? 📱
The new #HTB Track "Introduction to Android Exploitation" just landed!
8 beginner-friendly challenges & 1 machine to get started with mobile devices and #AppSec
#HackTheBox #CyberSecurity #InfoSec #Pentesting
3
72
228
Show this thread
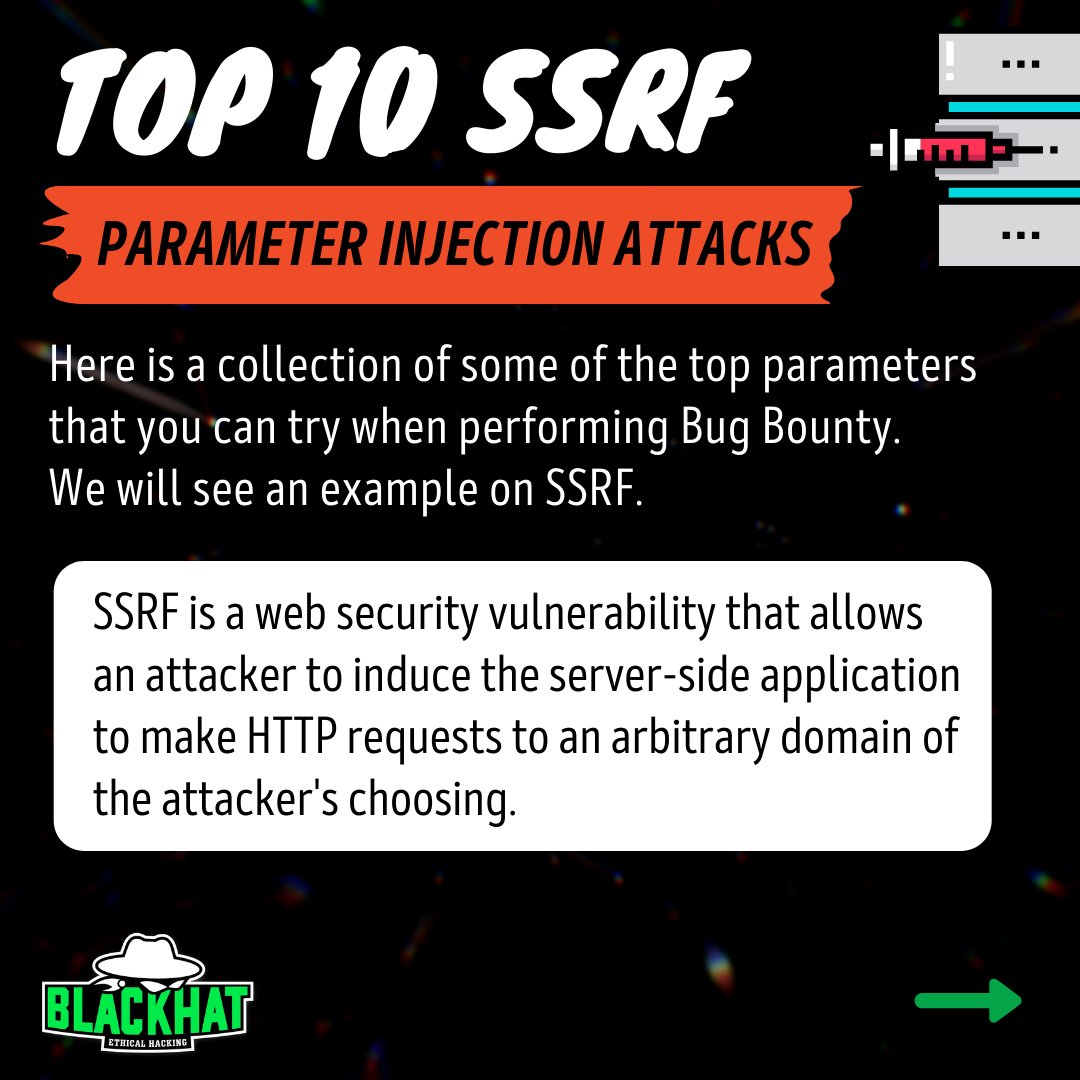
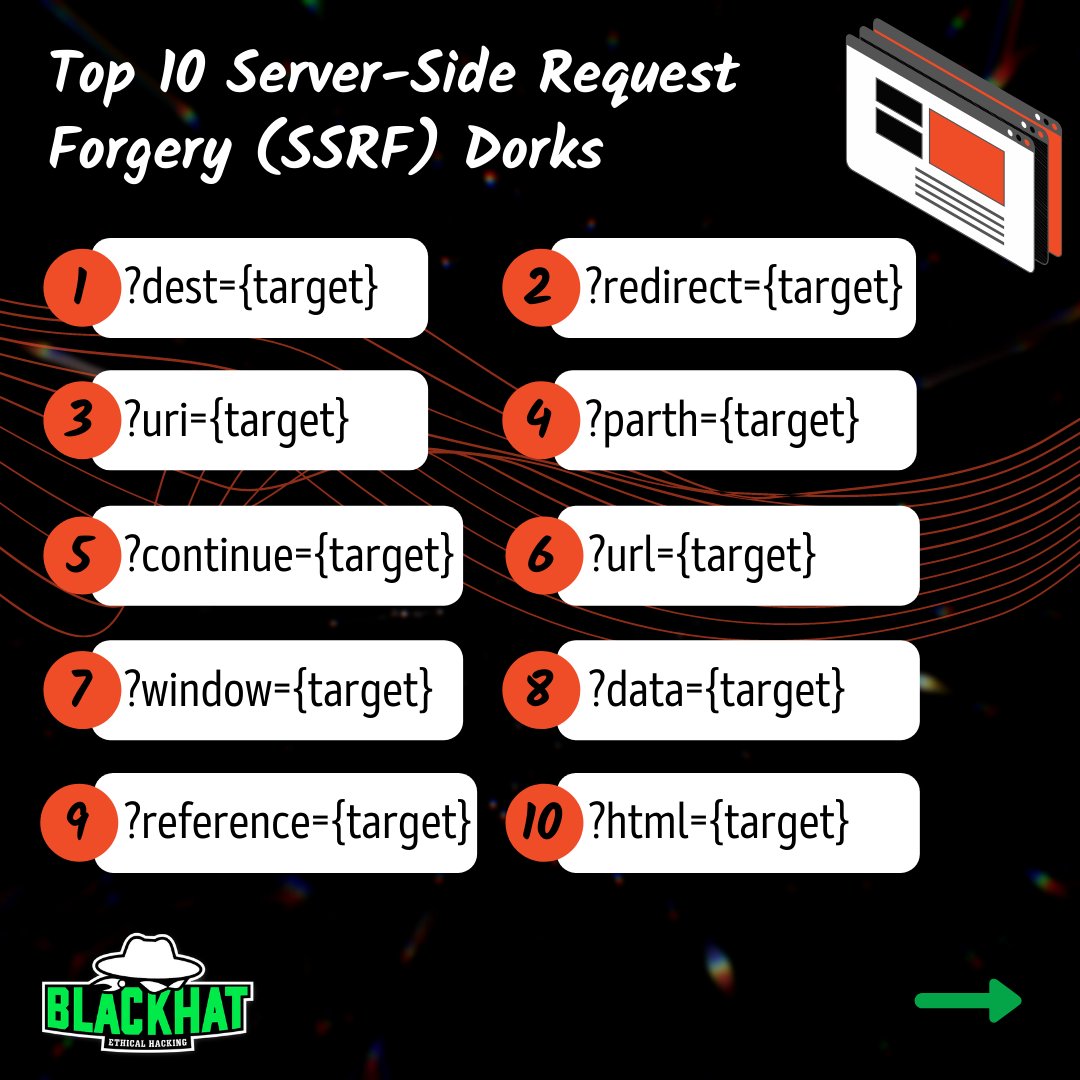
Top 10 SSRF Parameter Injection Attacks
Some top parameters that you can try when performing Bug Bounty or to test your application for such weaknesses. We'll see an example on SSRF
#infographics #ssrf #bugbounty #informationsecurity #infosec #cybersecurity #offensivesecurity
62
85
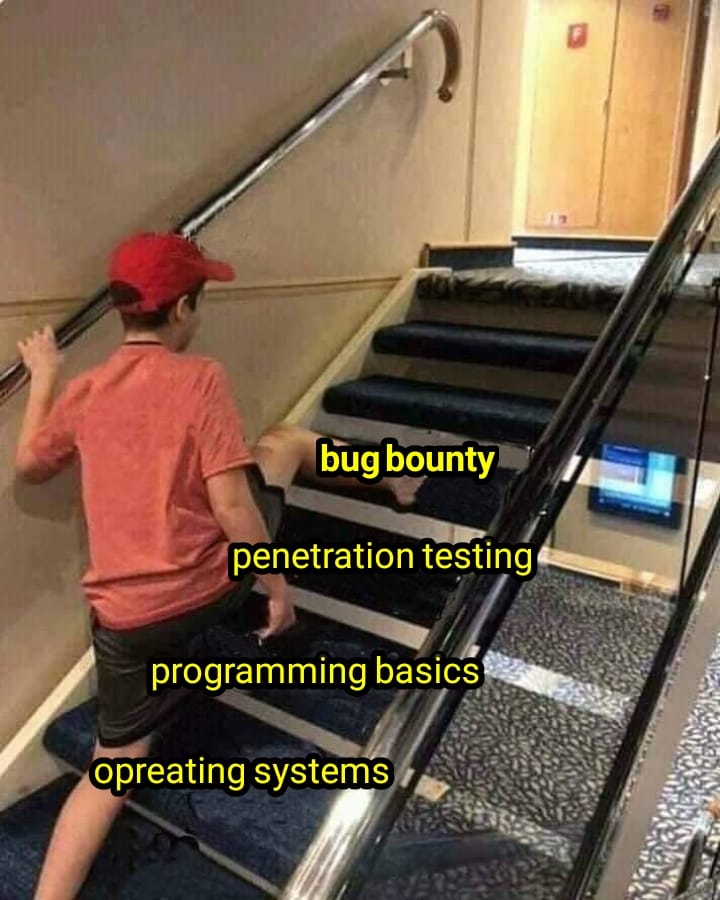
2022 Cybersecurity roadmap with the amazing
YouTube: youtu.be/mS7qWC3CbOU
#cyber #cybersecurity #kalilinux #oscp #hacking #ethicalhacking #python #golang

10
72
245