NIST Overhauls “Security and Privacy Controls” and Emphasizes VDP as a Best Practice
Back in 2005, the Computer Security Resource Center (CRSC) published NIST 800-53: the “Security and Privacy Controls for Information Systems and...
NIST Overhauls “Security and Privacy Controls” and Emphasizes VDP as a Best Practice
8 High-impact Bugs and How HackerOne Customers Avoided a Breach: SQL Injection
8 High-Impact Bugs and How HackerOne Customers Avoided a Breach: Information Disclosure
8 High-Impact Bugs and How HackerOne Customers Avoided a Breach: Privilege Escalation
Grand Rounds VP InfoSec: Achieving SOC 2 Type II Compliance with Hacker-Powered Security
Grand Rounds is an innovative new healthcare company using hacker-powered security for better, more effective...
What the California Consumer Privacy Act Means For You
The collection of personal data and the privacy issues surrounding it have been a hot topic the past several...
Hacker-Powered Security, Government Support Needed to Protect Financial Services Consumers from Application Vulnerabilities
What is the current state of security in the financial sector? How can governments contribute to this security...
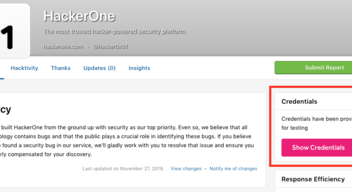
Easy and secure Credential Management
The new credential management functionality enables program owners to share credentials with hackers in the...