How does Cyber Immunity works in practice?
We explain the concept of a microkernel. How does it relates to the principle of minimizing the trusted code base (TCB)? kas.pr/j35v
#cyberimmunity #kasperskyos #microkernel
Kaspersky
@kaspersky
Kaspersky is the world’s largest privately held vendor of Internet security solutions for businesses and consumers. For support, visit support.kaspersky.com
kaspersky.comJoined February 2008
Kaspersky’s Tweets
OUT NEXT WEEK
Ethical hackers exist! 💻 Companies even pay them 💰💸 to hack their systems. 🖧 But why?
📽️Stay tuned!!
#WhiteHat #BugBounty #Xel
2
3
10
Want to learn more about cybersecurity, discuss security news in a community of like-minded people🧑🤝🧑 as well as our experts?
Join our Club on Discord 👉 kas.pr/qgs4
A global community of people interested in cybersecurity and related topics🎤

1
4
15
Hacking’s adrenaline rush can be addictive. But many believe black-hat (illegal) hackers can develop a moral compass and learn to use their skills for good – especially if authorities intervene when they’re young!!!👇
2
4
9
We recently released 𝗧𝗿𝗶𝗮𝗻𝗴𝗹𝗲_𝗰𝗵𝗲𝗰𝗸 – a free tool which scans iOS backups and also run checks for Operation Triangulation indicators.
Learn more and download here 👇 #IOSTriangulation
7
13
We've analyzed data from various sources, including the dark web, and uncovered 97 families operating through the Malware-as-a-Service (MaaS) model since 2015. 🕵️♀️🔍
To learn more about our discoveries, read our latest report 👉kas.pr/2bi9
GIF
4
Unlock the Future of Transportation! From connected autonomous vehicles (CAVs) to smart cities to integrated supply chains. Witness the disruption of cutting-edge technologies in action.
Register now!👉kas.pr/ofm8

1
#Cryptojacking could be costing your business and the Earth🌍
In a world of high emissions and energy bills, illegal cryptocurrency mining is the last thing business needs. Act now to avoid being exploited.👇kas.pr/ns38
1
2
Thrilling news! 🏆
💬 «Kaspersky has shown impressive results in the first quarter this year, continuing to validate 100% protection levels constantly developing and improving its products» Simon Edwards, CEO of SE Labs.

1
2
Stealing #crypto is hardly new in the criminal world, but new techniques are continually being developed & deployed by attackers.
#DoubleFinger is a multi-stage loader which uses steganography & modified binaries to deploy GreetingGhoul & Remcos.
More ⇒ kas.pr/6ufi

1
4
13
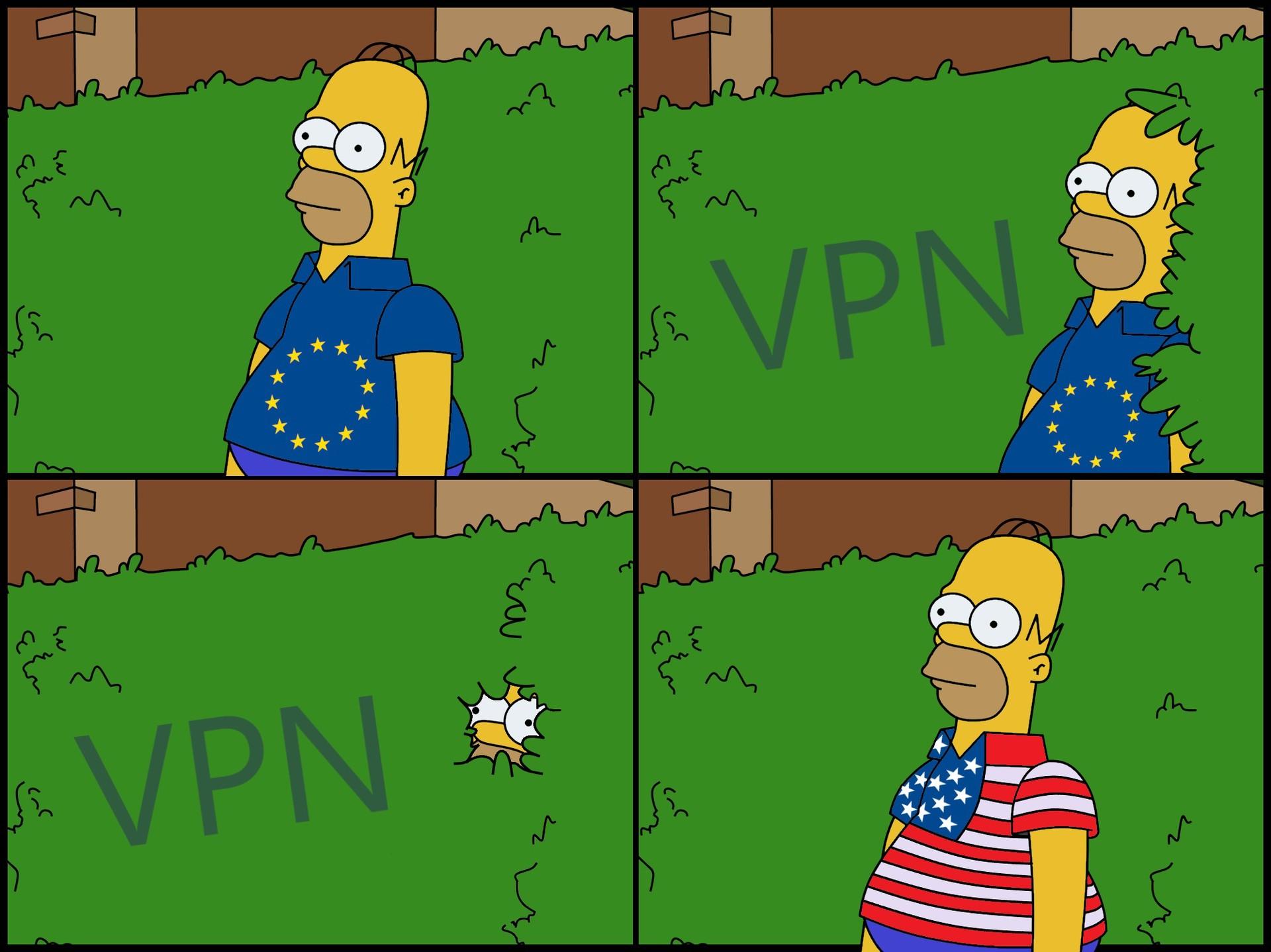
VPN's are great, but having to download apps for each device is time-consuming and messy.
Instead, why not install a VPN on your router? That way you get all the benifits of a #VPN, without the rigmarole. Learn how here ⇒ kas.pr/8ztk #Privacy #HowTo
9
29
It's been four LONG years, but finally we're bring back! From world renowned speakers to ground-breaking original research, you'll find it all at the Security Analyst's Summit, 2023.
Check it out ⇒ youtu.be/yFdcNupjKU0

2
1
3
How are #hackers currently targeting the #crypto industry? Who are they targeting?🕵 How can you protect your #company's systems from #cryptothreats? Find out in this #webinar 👉 kas.pr/1p36

1
1
1
Attention all cybersecurity enthusiasts! Get ready for our groundbreaking online event: "Unveiling the Darknet's Malware-as-a-Service model."
Register for free: 👉 kas.pr/57e6
#CybersecurityEvent #Darknet #Malware #Kaspersky

1
9
19
Saudi Arabian girls’ gaming 🎮 community GCON helps girls🛊feel confident 😎 and comfortable gaming, and facilitates global opportunities in game design and eSports. Listen: #Podcast #GirlsGaming #GCON
🔊fastforward.podbean.com
6
OUT NEXT WEEK
Ethical hackers exist! 💻 Companies even pay them 💰💸 to hack their systems. 🖧 But why?
📽️Stay tuned!!
#WhiteHat #BugBounty #Xel
1
2
6
New Course Alert!📚
Suricata for Incident Response and Threat Hunting
👉kas.pr/9gmi
Suricata is the foundation for effective intrusion detection and prevention. NOW it’s more crucial than ever for businesses, enterprises or cybersecurity consultancies!!
1
8
Join us today to learn how to enhance incident responses for large-scale networks and mitigate the impact of cyber attacks. Don't miss out on valuable insights from our industry expert Konstantin Sapronov.
🌐 Register now:
1
5
Have you ever wondered what our Earth will look like in 2050? Insanely, we have our own project that shows what a shocking future awaits humanity?
What do you think?
See more here👉 kas.pr/5jdf!
1
7
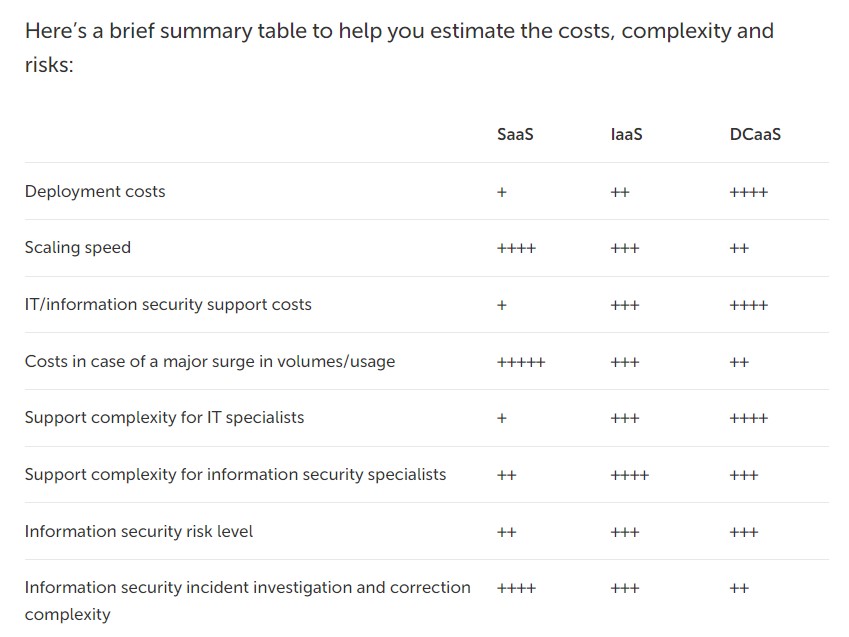
Cloud technologies differ in terms of costs and risks, so what's the ideal #cloud strategy for your #business? ➡️ kas.pr/wez9
#cybersecurity #SAAS #technology
1
7
Are you curious to know how #2FA works and why it's essential for your #online accounts? 🤔
Check it out 🔐⬇️
#cybersecurity #privacy #socialmedia #authenticator
kas.pr/j8xc
1
1
🚨 Beware #YouTubers! #Hackers can access your channel without #passwords with a sneaky trick called a "pass-the-cookie" attack.
🛡️ Tips to protect yourself 👉 kas.pr/rrv6
7
16
Surf the web in confidence! The Internet is certainly convenient and useful, but using it has made our data more vulnerable than ever before. kas.pr/mf2p
Worry not, let our privacy checker be your guide to ensuring your data stays secure. Surf safe & sound with us!🏄♀️

2
6
ICYMI - MaaS or 'Malware-as-a-Service' is a popular way for #malware developers to generate handsome returns.
In our upcoming webinar, we look at the latest tactics & trends of these groups, as well as how to defend against them.
Learn more & register ⇒ kas.pr/2q4a

3
Stealing #crypto is hardly new in the criminal world, but new techniques are continually being developed & deployed by attackers.
#DoubleFinger is a multi-stage loader which uses steganography & modified binaries to deploy GreetingGhoul & Remcos.
More ⇒ kas.pr/6ufi
2
11
Modern cars are no longer just a means of transportation. They can manage everything for drivers!
In this webinar we explore:
• Threat landscape changes
• Top threats in automotive industry
• Automotive security
• Security Trends
Find our more here👉
2
6
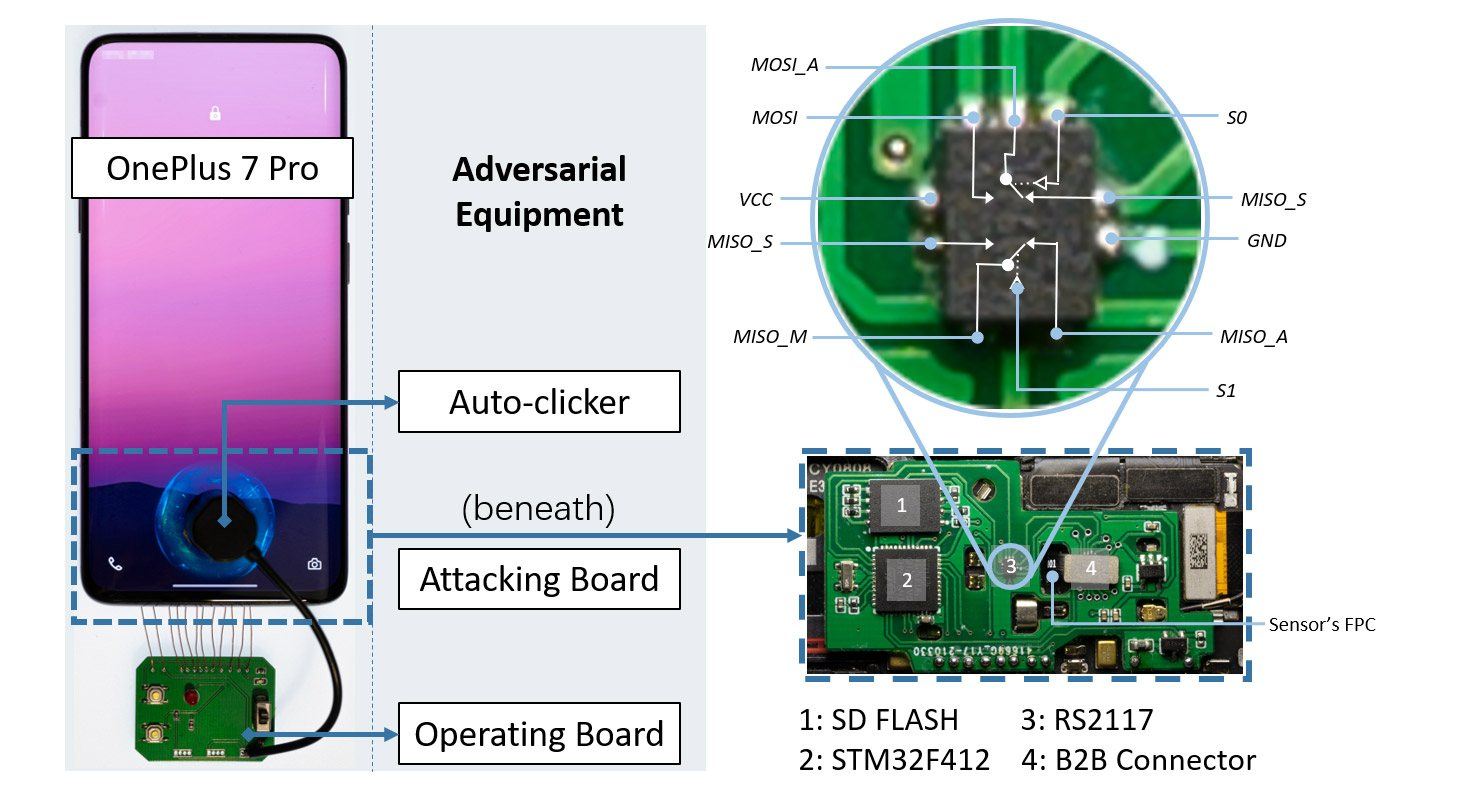
Biometrics, they're totally unique, so unbreakable, right? Well, Chinese researchers have recently found there's actually a way to 'brute-force' almost any fingerprint-protected #Android smartphone.
They're calling it 'BrutePrint'. Full story ⇒ kas.pr/2dgi
7
18
How does Cyber Immunity works in practice?
We explain the concept of a microkernel. How does it relates to the principle of minimizing the trusted code base (TCB)? kas.pr/j35v
#cyberimmunity #kasperskyos #microkernel
1
5
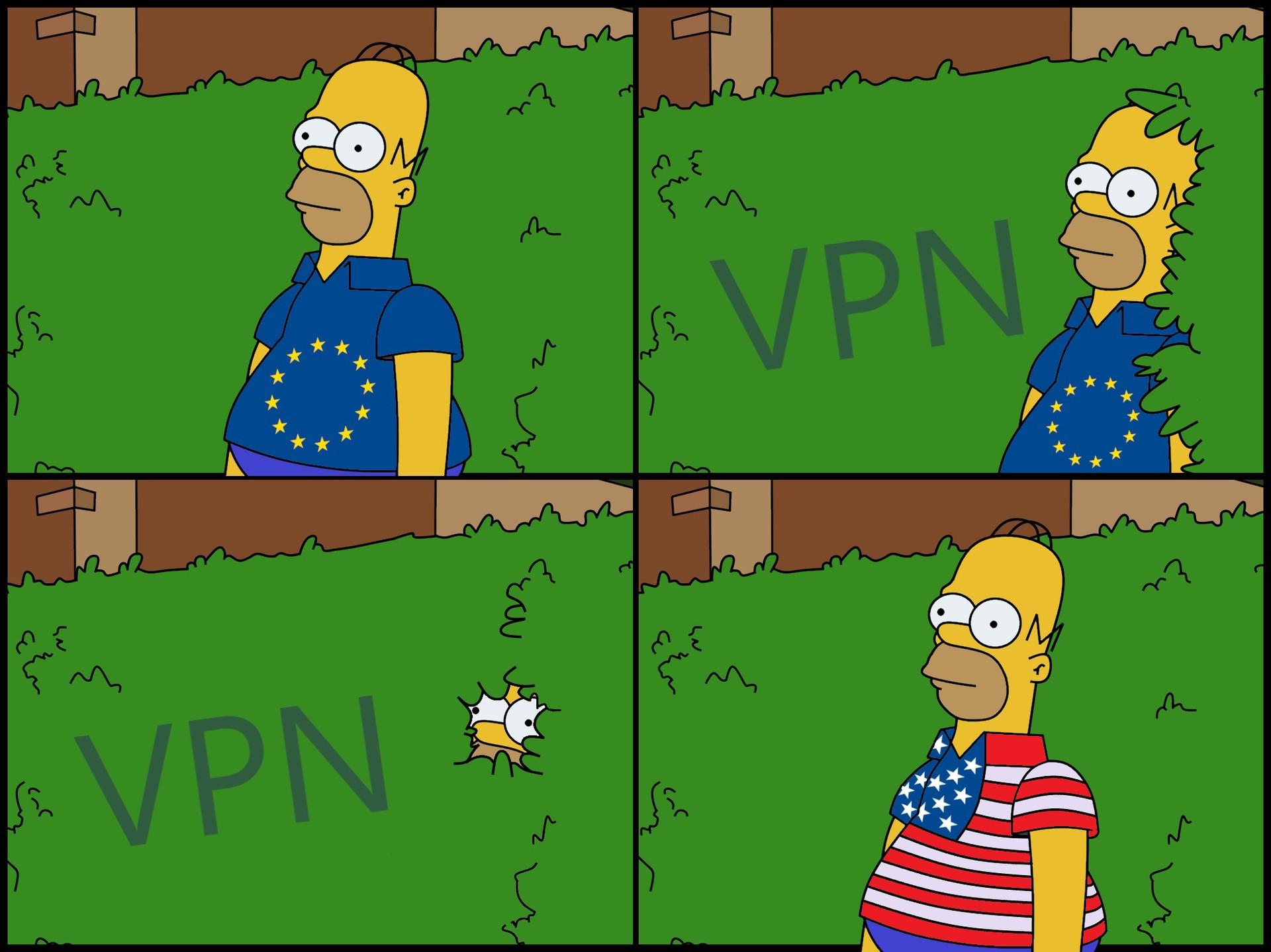
VPN's are great, but having to download apps for each device is time-consuming and messy.
Instead, why not install a VPN on your router? That way you get all the benifits of a #VPN, without the rigmarole. Learn how here ⇒ kas.pr/8ztk #Privacy #HowTo
1
8
36
Do you know what your #competitors are spending on #cybersecurity?💸💸 Our #ITsecurity #calculator can help 👉 kas.pr/129e
1
1
4
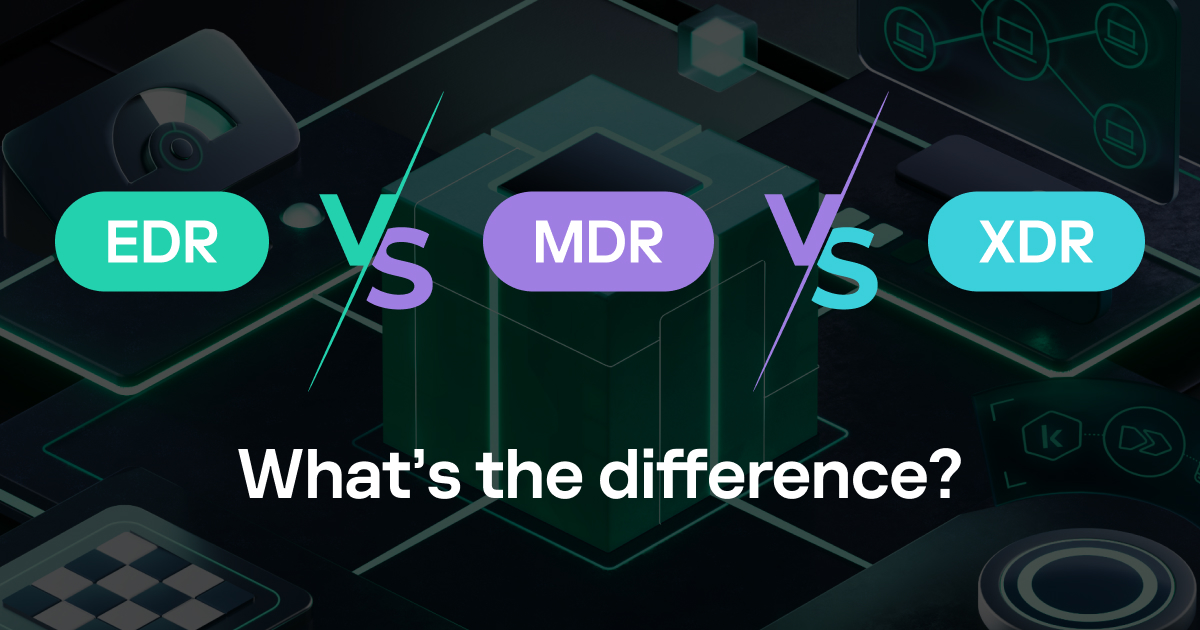
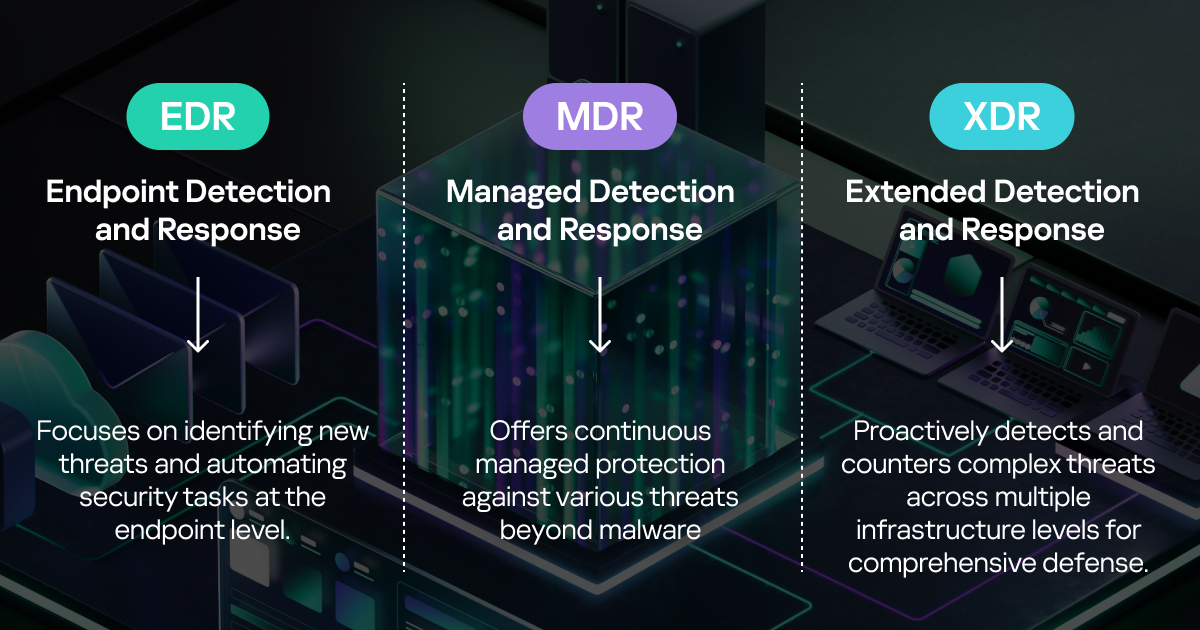
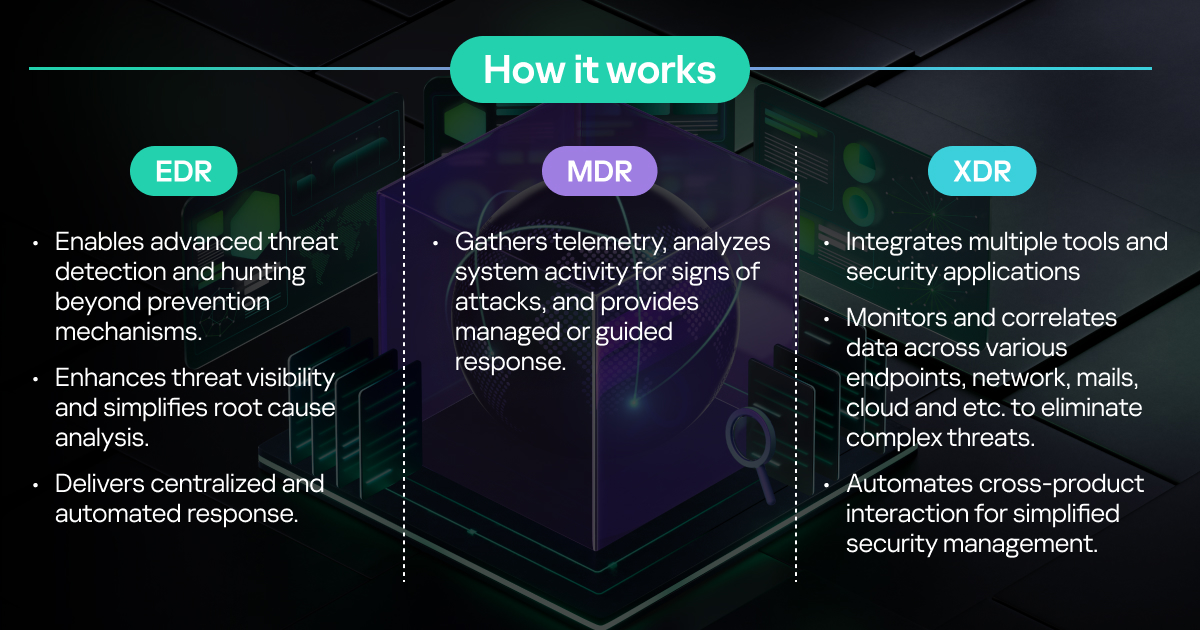
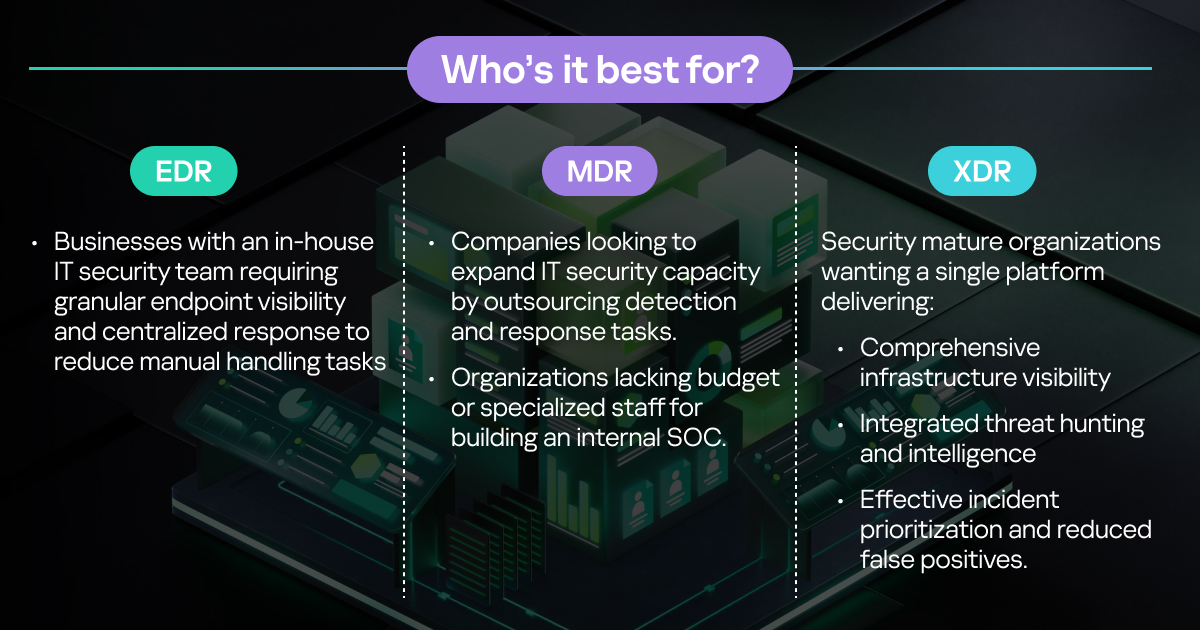
Unlock the power of #EDR, #MDR, and #XDR! 🚀
Explore the key differences, unique features and capabilities of these #security solutions, and find out which one is right for your #organization 🛡️
Learn more ➡️ kas.pr/5tw7
1
8
#Cryptojacking could be costing your business and the Earth🌍
In a world of high emissions and energy bills, illegal #CryptoCurrency mining is the last thing business needs.
Learn more ⇒ kas.pr/ns38
2
3
Surf the web in confidence! The Internet is certainly convenient and useful, but using it has made our data more vulnerable than ever before.
Worry not, let our privacy checker be your guide to ensuring your data stays secure. Surf safe & sound with us!🏄♀️ kas.pr/mf2p
1
8
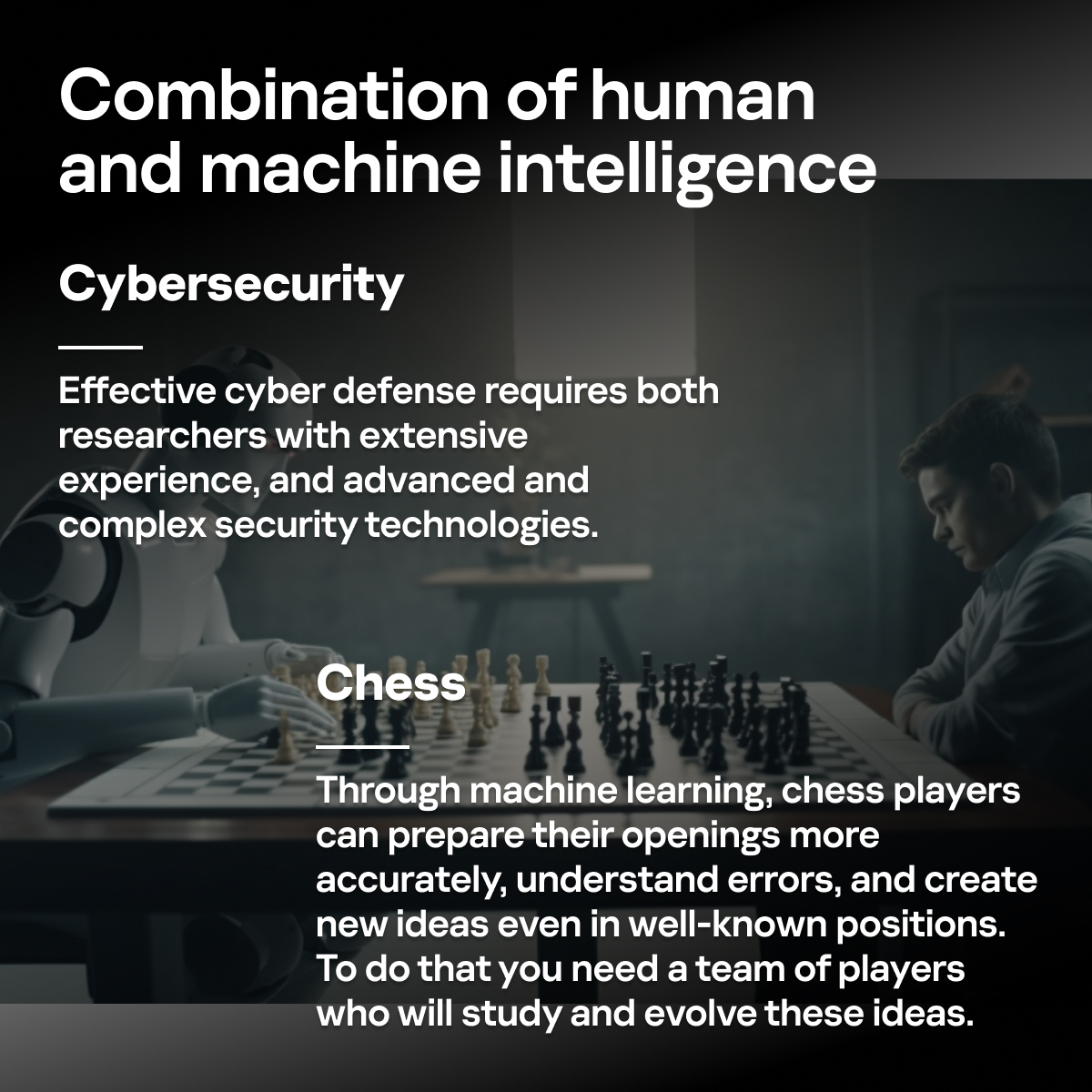
Chess players from Europe & Africa have gathered in Berlin for the thrilling Armageddon Championship Series 2023, & we're proud to be a part of it with ♟️
What are the similarities between chess & cybersecurity?⬇️
Learn more 👉 kas.pr/7kff


3
8
VPN's are great, but having to download apps for each device is time-consuming and messy.
Instead, why not install a VPN on your router? That way you get all the benifits of a #VPN, without the rigmarole. Learn how here ⇒ kas.pr/8ztk #Privacy #HowTo
5
36
New Course Alert!📚👉kas.pr/9gmi
Suricata is the foundation for effective intrusion detection and prevention. NOW it’s more crucial than ever for businesses, enterprises or cybersecurity consultancies!!

1