USCYBERCOM Cybersecurity Alert
@CNMF_CyberAlert
This is Cyber National Mission Force’s alert mechanism to contribute to our shared global cybersecurity (Following, retweets and links do not equal endorsement)
Joined November 2018
USCYBERCOM Cybersecurity Alert’s Tweets
🚨Mitigate Iranian MOIS cyber actor #MuddyWater's suite of tools with joint Malware Analysis Report. Malware used for espionage & more--exposed & attributed in Jan ‘22 to Iran's Ministry of Intel & Security here: Virustotal.com/en/user/CYBERC.
Quote Tweet
 .@CISAgov, @FBI, @CNMF_CyberAlert, @NCSC, and @NSACyber have issued a joint advisory detailing malicious cyber activities conducted by Iranian government-sponsored APT actors known as #MuddyWater. Learn more at go.usa.gov/xzcp4 #Cybersecurity #InfoSec #CyberSquad
.@CISAgov, @FBI, @CNMF_CyberAlert, @NCSC, and @NSACyber have issued a joint advisory detailing malicious cyber activities conducted by Iranian government-sponsored APT actors known as #MuddyWater. Learn more at go.usa.gov/xzcp4 #Cybersecurity #InfoSec #CyberSquad
3
61
74
Review this blog and check your networks for IOCs related to this ongoing malicious activity. Actionable threat sharing among public-private partners makes a difference against adversary intrusions. Good work by all involved!
8
91
165
Show this thread
MuddyWater and other Iranian MOIS APTs are using DNS tunneling to communicate to its C2 infrastructure; if you see this on your network, look for suspicious outbound traffic.
4
35
67
Show this thread
MOIS hacker group MuddyWater is using open-source code for malware. These samples are indicators that a network has been compromised.
1
29
65
Show this thread
Iranian MOIS hacker group #MuddyWater is using a suite of malware to conduct espionage and malicious activity. If you see two or more of these malware on your network, you may have MuddyWater on it: Virustotal.com/en/user/CYBERC. Attributed through
26
386
518
Show this thread
Topics to follow
Sign up to get Tweets about the Topics you follow in your Home timeline.
Carousel
🚨 Active scanning of Apache HTTP Server CVE-2021-41773 & CVE-2021-42013 is ongoing and expected to accelerate, likely leading to exploitation. Please patch immediately if you haven’t already—this cannot wait until after the weekend. Read more: us-cert.cisa.gov/ncas/current-a

48
293
308
Mass exploitation of Atlassian Confluence CVE-2021-26084 is ongoing and expected to accelerate. Please patch immediately if you haven’t already— this cannot wait until after the weekend.
65
2,413
3,985
Three common sources of compromise in #Kubernetes are supply chain risks, malicious threat actors, and insider threats. #KnowingIsHalfTheBattle💪
#KubernetesClusters #Cybersecurity #OpenSource
18
109
105
Quote Tweet
10
117
187
Quote Tweet
.@CISAgov is aware of the likelihood that cyber threat actors are attempting to exploit CVE-2021-21985, a remote code execution vulnerability in VMware vCenter Server and VMware Cloud Foundation. Learn more at go.usa.gov/x6bA5.
10
144
202
Do you have that #FridayFeeling you’re being hacked? Read ’s Best Practices for Mapping to better understand adversary behavior and defend your networks. go.usa.gov/x6bxs
2
27
42
Updated eviction guidance released by . Follow these steps to effectively remove known APT actor from networks.
Quote Tweet
 We have released eviction guidance related to the ongoing SolarWinds Orion incident and related campaign activities affecting U.S. government agency networks, CI entities, and private sector organizations.
View our updated guidance: go.usa.gov/xHHFv
We have released eviction guidance related to the ongoing SolarWinds Orion incident and related campaign activities affecting U.S. government agency networks, CI entities, and private sector organizations.
View our updated guidance: go.usa.gov/xHHFv
5
61
102
5
103
217
., released 8 files attributed to Russian SVR/APT 29. Upload includes new malware variants of GoldMax, GoldFinder, Sibot and associated files which were used to compromise a single victim network. #SolarWinds virustotal.com/en/user/CYBERC
2
50
69
Show this thread
., , link Russian SVR/APT 29 actors to network infiltration through #SolarWinds supply chain compromise and GoldenSAML exploitation of M365. Read the report here: us-cert.cisa.gov/ncas/analysis-

22
153
225
Show this thread
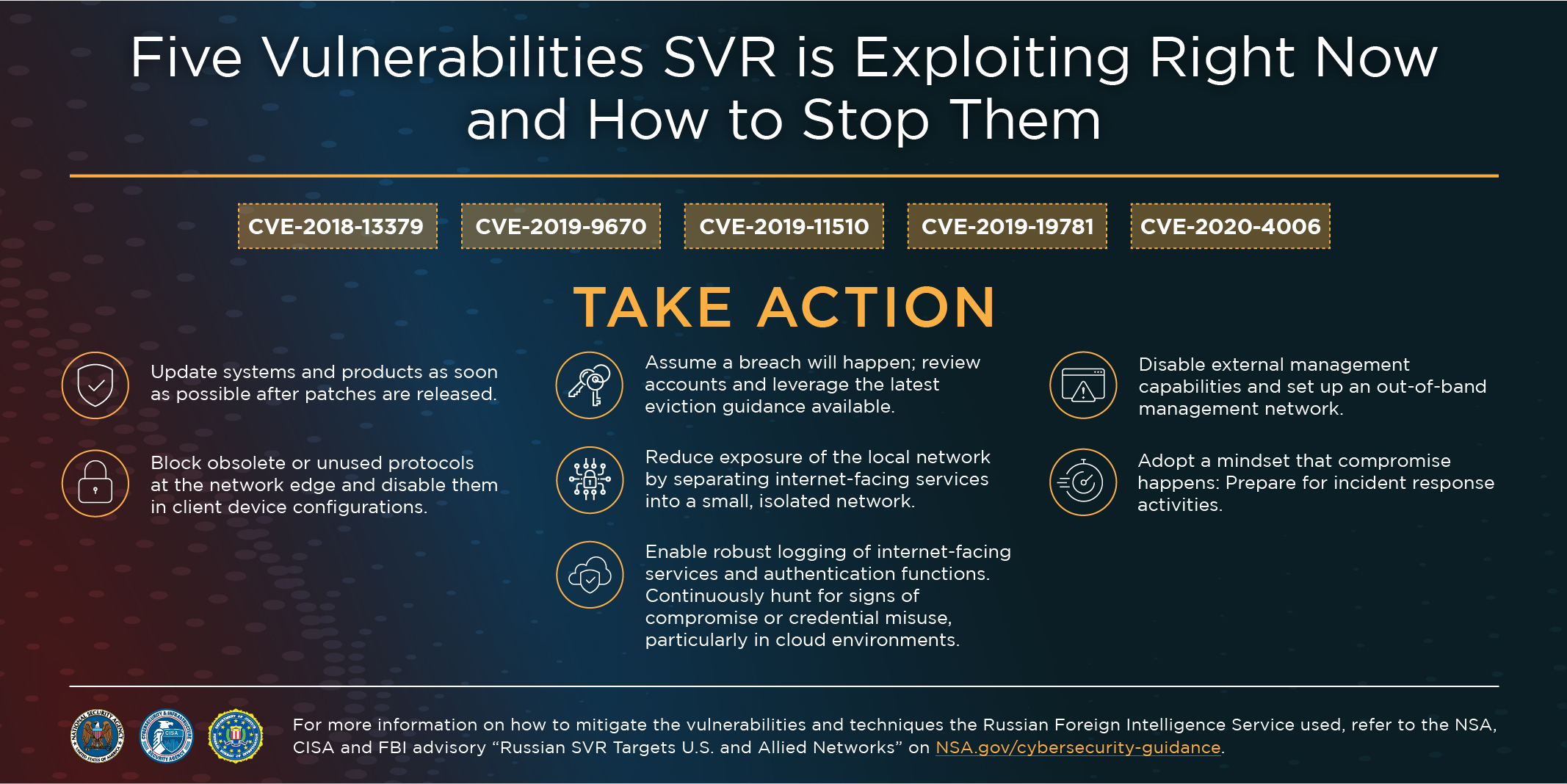
Russian Foreign Intelligence Service (SVR) cyber actors are exploiting five publicly known vulnerabilities to target U.S. and allied critical networks. Review our joint #cybersecurity guidance with and and apply the mitigations to stop them: nsa.gov/News-Features/
103
1,429
1,996
Microsoft has released #security updates for #vulnerabilities found in Exchange Server 2013, Exchange Server 2016, and Exchange Server 2019.
1
63
87
Quote Tweet
APT actors are scanning for vulnerabilities with Fortinet FortiOS to gain access to multiple government, commercial, and technology services networks – read our joint cybersecurity advisory with the @FBI: go.usa.gov/xHx4D

7
155
191
“Foreign malign influence is an enduring challenge facing our country,” said Director of National Intelligence Avril Haines. “These efforts by U.S. adversaries seek to exacerbate divisions and undermine confidence in our democratic institutions." odni.gov/index.php/news
17
76
130
Microsoft has released a new, one-click mitigation tool, the Microsoft Exchange On-Premises Mitigation Tool, to help customers who do not have dedicated security or IT teams to apply security updates for Microsoft Exchange Server. Learn more: msft.it/6015VKNpL

11
527
796
❗ NEWLY ISSUED GUIDANCE is available on ’s Microsoft Exchange Vulnerabilities web page. Visit go.usa.gov/xsyVk to review the latest guidance and resources from Microsoft for remediating the exploitation of Exchange vulnerabilities.
#Cybersecurity #InfoSec #IT
5
133
149
Anyone that has Exchange on-prem exposed to the internet on 80/443 should consider checking into CVE-2021-27065 immediately. I received the patch KB5000871 & installed at 16:30EST but still saw a box popped. Box was hit on the 28th of Feb so this HAS been happening awhile. 1 of 2
9
167
314
Show this thread
Patches released by for multiple Exchange #CVE. Immediate action is critical, as some are currently being exploited in the wild. Exploits enable unauthenticated RCE when chained.
6
97
133
#BendyBear malware suspected to have compromised several East Asian governments through actions similar to BlackTech #WaterBear incidents in the past
Quote Tweet
Today, we exposed "BendyBear," one of the most sophisticated, well-engineered and difficult-to-detect samples of shellcode employed by an APT, says the Unit 42 researcher who analyzed it. bit.ly/3aH1ABi

17
93
125
Multiple agencies collaborated to untether victim computers from #Emotet, effectively disrupting the botnet responsible for hundreds of millions of dollars in damage worldwide. Great job!
Quote Tweet
One of the world’s most dangerous malware botnet #Emotet disrupted in international cyber operation
@USAO_MDNC @FBI @FBICharlotte @Europol @Eurojust @bka @PolitieLE @GStA_FFM_ZIT
justice.gov/opa/pr/emotet-
9
43
125
We recommend applying patches as soon as available. This is a far more dangerous #Sudo vulnerability than seen in the rescent past.
Quote Tweet
Got Root? You do now with CVE-2021-3156 privilege escalation in SUDO. Exploitable Heap-based buffer overflow in a utility that is available in almost all major linux/unix OS versions. twitter.com/qualys/status/…
8
199
298
Russian state-sponsored cyber actors are exploiting #vulnerability CVE-2020-4006 affecting VMware Workspace ONE Access.
Quote Tweet
13
99
160
"The National Cyber Force is a joint Defence and capability, giving the UK a world class ability to conduct cyber operations." -Defence Secretary Ben Wallace
gchq.gov.uk/news/national-
Quote Tweet
.@US_CYBERCOM warmly welcomes our newest partners in cyber operations: the UK National Cyber Force. We look forward to working with the NCF against cyber threats. twitter.com/GCHQ/status/13…
6
14
43
⚠️ New malware variant – Zebrocy – identified by and . Learn more at go.usa.gov/x7jbu.
#Zebrocy #Cybersecurity #InfoSec #Malware
8
79
90
. and identified #Zebrocy implant used to target victims in Eastern Europe and Central Asia, including embassies and ministries of foreign affairs.
View samples on 's Virus Total: virustotal.com/en/user/CYBERC and MAR at us-cert.cisa.gov/ncas/analysis-
5
71
103
⚠️ New malware variant – ComRAT – identified by and . Learn more at go.usa.gov/x7jj4.
#ComRAT #Cybersecurity #InfoSec #Malware
4
52
76
An implant dropper dubbed #ComRATv4 recently attributed by and to Russian sponsored APT, Turla. It was likely used to target ministries of foreign affairs and national parliament.
continues to disclose #malware samples on: virustotal.com/en/user/CYBERC

87
417
1,050
The public and private sectors are united against ransomware, especially those actors targeting medical facilities during a pandemic. This report is just one example of the work being done to address the current threat. twitter.com/Trellix/status
This Tweet is unavailable.
9
169
317
., and released the Kimsuky Cybersecurity Advisory, a summary of #DPRK malicious cyber acitivity posing as Google, Yahoo mail services, and South Korean reporters, targeting Japan, South Korea, and the United States.
us-cert.cisa.gov/ncas/alerts/aa

6
174
247
.U.S. networks are constantly being scanned, targeted, and exploited by Chinese state-sponsored cyber actors. Take action and mitigate against these exploits used in their hacking operations.
9
87
138
Quote Tweet
“No country has weaponized its cyber capabilities as maliciously or irresponsibly as Russia, wantonly causing unprecedented damage to pursue small tactical advantages and to satisfy fits of spite.” —Assistant Attorney General Demers.

read image description
ALT
6
55
91
The #SlothfulMedia implant has the ability to run commands, kill processes, invoke a remote shell, add and delete registry values, take screen shots and interact with the file system.
For more info see 's MAR us-cert.cisa.gov/ncas/analysis-
Quote Tweet
 @CISAgov and @CNMF_CyberAlert have a released a Malware Analysis Report on SLOTHFULMEDIA—this remote access trojan is used by a sophisticated cyber actor. Check out the report at go.usa.gov/xGAg3 for more information, including #IOCs.
#Malware #Cybersecurity #InfoSec
@CISAgov and @CNMF_CyberAlert have a released a Malware Analysis Report on SLOTHFULMEDIA—this remote access trojan is used by a sophisticated cyber actor. Check out the report at go.usa.gov/xGAg3 for more information, including #IOCs.
#Malware #Cybersecurity #InfoSec
3
86
100





















