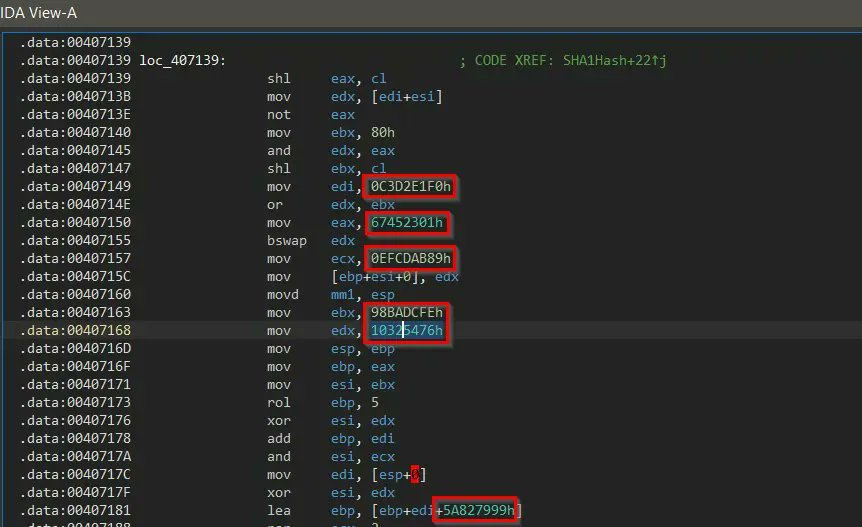
Great post by about techniques for invoking functions directly from assembly: IDA Appcall, Dumpulator and Unicorn Engine
research.checkpoint.com/2022/native-fu
#reverseengineering #malwareanalysis #informationsecurity #cybersecurity #assembly
Search timeline
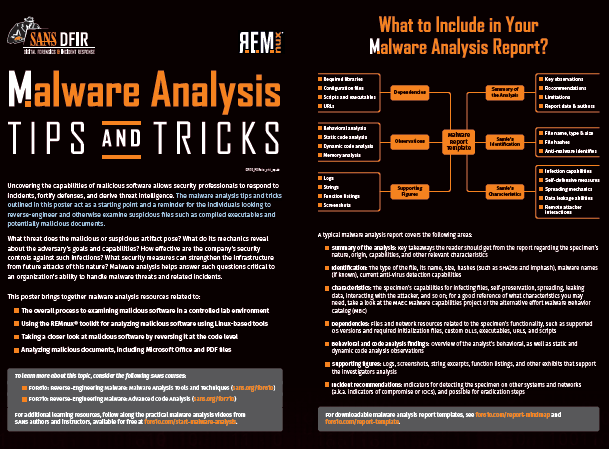
NEW #DFIR POSTER | #MALWAREANALYSIS:TIPS & TRICKS by #FOR610 course author
This poster provides a starting point to reverse-engineer & examine suspicious files like compiled executables & potentially malicious documents.
DOWNLOAD IT NOW! 👉 sans.org/u/1mT9
15
23
SEVulDet: Semantics-Enhanced Learnable Vulnerability Detector ift.tt/9eStJvO #security #opensource #cybersecurity #malware #cyber #pentesting #malwareanalysis #infosec #redteam #malwarehunting #hacking #infosec #threathunting #bugbounty #tools #offensivesecurity
3
1
NEW #DFIR POSTER | #MALWAREANALYSIS:TIPS & TRICKS by #FOR610 course author
This poster provides a starting point to reverse-engineer & examine suspicious files like compiled executables & potentially malicious documents.
DOWNLOAD IT NOW! 👉 sans.org/u/1mT9

1
13
20
6
25
144
Show this thread
1
Users of #Samsung and #LG devices are at risk of being attacked by this malware.
.
.
#malware #malwarebytes #malwareanalysis #samsung #LG #attack #smartphones #smartphone #virus
read image description
ALT
1
Check out our latest blog and learn about Malware Patrol's new OSINT feeds.
#cybersecurity #networksecurity #malware #threathunting #redteam #blueteam #malwareanalysis #firewall #SOC #pentesting #incidentresponde #CISO #threatintelligence #CTI
malwarepatrol.net/new-osint-data

1
3
FarsightAD: help uncovering (eventual) persistence mechanisms ift.tt/y8swCek #security #opensource #cybersecurity #malware #cyber #pentesting #malwareanalysis #infosec #redteam #malwarehunting #hacking #infosec #threathunting #bugbounty #tools #offensivesecurity
5
2
Quote Tweet
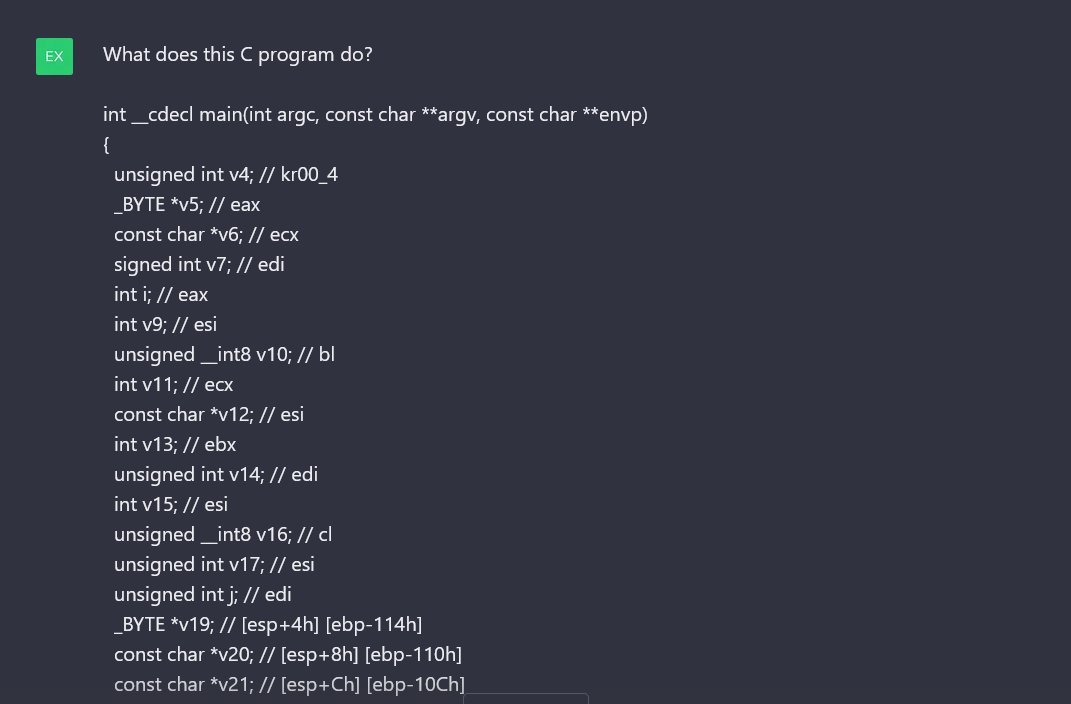
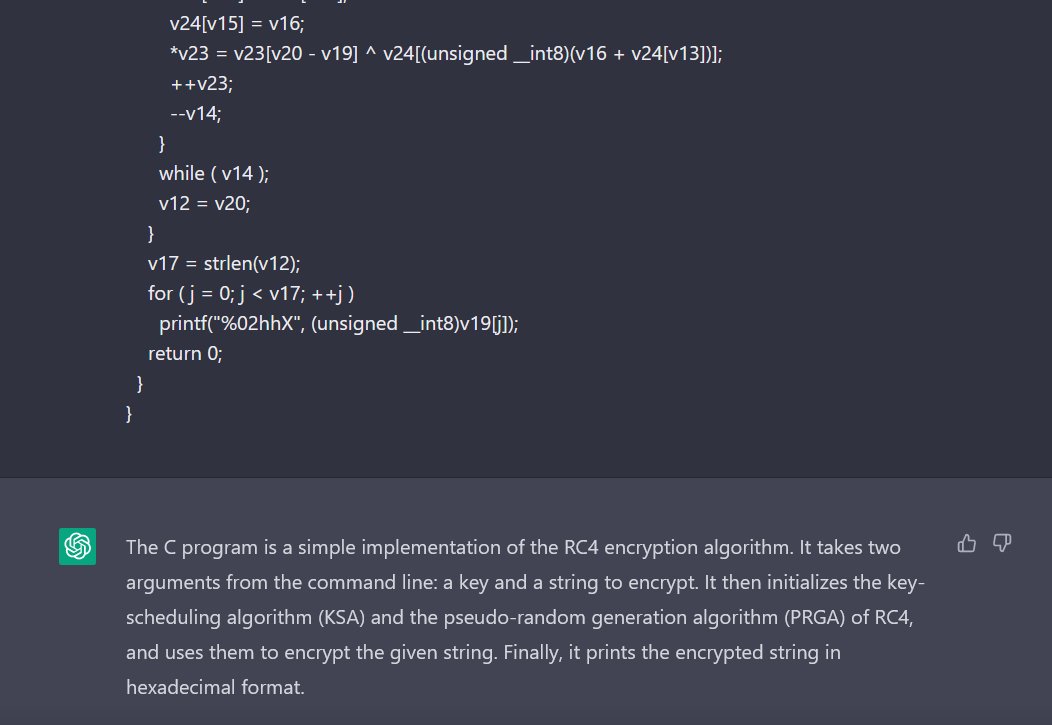
Step 1: open a binary in IDA and press F5
Step 2: paste the decompiled code into OpenAI's chatbot
Someone's job just got way easier.
Show this thread
ADFSRelay: NTLM Relaying Attacks Targeting ADFS ift.tt/IcQsBgN #security #opensource #cybersecurity #malware #cyber #pentesting #malwareanalysis #infosec #redteam #malwarehunting #hacking #infosec #threathunting #bugbounty #tools #offensivesecurity
5
3
Try Malware Patrol's threat data for Mikrotik routers: Malicious Domains, DNS-over-HTTPS servers, and Tor Exit Nodes. Sign up for a 7-day, full-access trial.
#cybersecurity #networksecurity #malware #threathunting #malwareanalysis #SOC
malwarepatrol.net/mikrotik-route

2
As notorious as it sounds, it is also called: WannaCryptor| Wanna Decryptor| WannaCrypt| CryptoWorm| and RansomWorm
#cybersecurity #malwareanalysis #cybernauts #onecyberthingadaywithcybersechaven
1
1
5
Show this thread
Pylirt - Python Linux Incident Response Toolkit ift.tt/eL1Pbud #security #opensource #cybersecurity #malware #cyber #pentesting #malwareanalysis #infosec #redteam #malwarehunting #hacking #infosec #threathunting #bugbounty #tools #offensivesecurity
1
Malware Detection using machine learning ift.tt/yAfj3Kl #security #opensource #cybersecurity #malware #cyber #pentesting #malwareanalysis #infosec #redteam #malwarehunting #hacking #infosec #threathunting #bugbounty #tools #offensivesecurity
3
3
ldapnomnom: Anonymously bruteforce Active Directory username ift.tt/y3LdcpP #security #opensource #cybersecurity #malware #cyber #pentesting #malwareanalysis #infosec #redteam #malwarehunting #hacking #infosec #threathunting #bugbounty #tools #offensivesecurity
1
4
3
Linux-based file servers are often integral to small, medium, and large businesses alike.
Contact Us: bit.ly/3CyjV1j
#eScan #malwareprotection #malware #malwareandbackup #cybersecurity #malwareremoval #malwareanalysis #antivirus #dataprotection #business #cyberattack

2
Intro to Defensive Security - I have just completed this room!Check it out: tryhackme.com/room/defensive #tryhackme #security #defensivesecurity #IncidentResponse #threatintelligence #malwareanalysis #DFIR #SOC #SIEM #SecurityOperationsCenter #defensivesecurityhq via
2
2
ImHex - Hex Editor For Reverse Engineers And Programmers..
Adds a node-based data processor, custom encodings though thingy files.
hackersonlineclub.com/imhex-hex-edit
#malwareanalysis #cyberintelligence #hackersonlineclub #security #infosec #cybersecurity
1
1
Get Ready for a Live #Webinar on #MalwareAnalysis. This Friday, 9th December, from 12:30 PM - 01:30 PM. Learn about Trojan Horse and its Static and Dynamic Functionality. This webinar will be hosted by Mr. Amit Kumar (Security Analyst).
< craw-in.zoom.us/meeting/regist >